Folder Lock Key Serial
Posted in:admin
Folder Lock Review Rating. By now it should be clear that encryption isnt just for security geeks and IT administrators. Folder Lock Key Serial' title='Folder Lock Key Serial' />You can take precautions to secure your own most sensitive files and folders by encrypting them. Some encryption utilities turn files and folders into encoded versions of themselves. Others create secure storage locations that act like standard drives or folders but can be locked, encrypting all of their contents. Still others maintain encrypted storage in the cloud. Most encryption utilities stick to just one of these functions. Folder Lock does all three things, and more, balancing ease of use with a wide range of features. As with most competing products, your 3. Folder Lock Key Serial' title='Folder Lock Key Serial' />Folder Lock 7. I tested indefinitely. You dont have to buy right away you can run the program 2. You also get free access to all updates until the next major point update. When version 8 comes out, you can either pay an update fee or just keep using the current version. What Is Encryption The Nazi government used a device called the Enigma Machine to encrypt sensitive military communications before and during World War II. With its rows of buttons and actuator wheels, the device looked quite impressive. Gear Box Computers provides freeware software downloads such as Wifi HotSpot, Wifi Key Finder, Windows Product Key Finder, Folder Vault Folder Locking, Hide and. Welcome To Serial Key. We are a digital agency that buys, sells and giveaways genuine serial keys of popular softwares. Get Started. 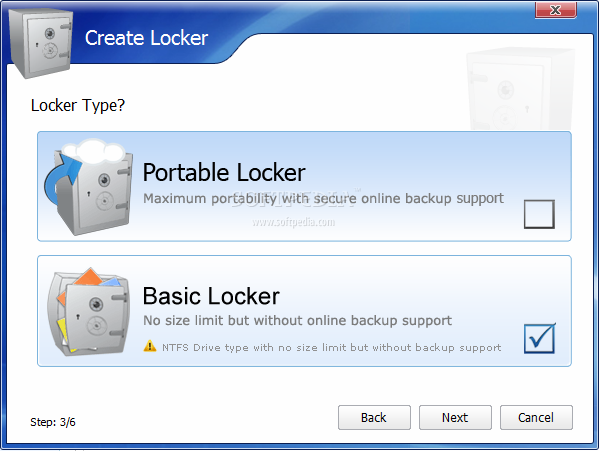 However, not only did the Allied forces crack the code, they managed to keep that fact from the enemy, so the Nazi generals kept sharing their strategies using the faulty encryption system. The resulting intelligence served the Allied forces well. Cryptographic algorithms used today have a certain connection to the old Enigma Machine, but of course theyre totally code based, with no steampunk buttons or wheels. Unless you have the password, theres no way to decrypt an encrypted document. No, you cant just try every possible password, not unless youre willing to wait for the heat death of the universe. In 2. 00. 1, the US government settled on Advanced Encryption Standard AES. Data Encryption Standard. With even more bits in its main security key, Bruce Schneiers Blowfish algorithm should be still more secure. Youre probably familiar with symmetric encryption algorithms, where the same key encrypts and decrypts a file. AES, Blowfish, and many other common algorithms are symmetric. With this kind of algorithm, you must keep the password a deep, dark secret, and only share it via secure channels. But theres another way. In a Public Key Infrastructure system, you get two keys, one public and one private. Bit Digital Signal Controller with Flash. Recommended alternative parts. TMS320F28377S The device has SIMILAR FUNCTIONALITY but is not functionally equivalent. If I want to send you a file, I look up your public key and use it for encryption you decrypt it with your private key. Public key cryptography is less common in small scale encryption utilities. Getting Started With Folder Lock. Installation of the product is quick and simple When you do pay up, youll receive a serial number and a registration key. Keep that serial number stored in a safe place. If you forget your master password, you can unlock the program by entering that serial number. If that last statement worries you, congratulationsyouve caught on to something. All of the encryption products Ive reviewed recently have no backdoor, no way for the company to decrypt your files. But since the company clearly has your Folder Lock serial number, it could conceivably be ordered to supply it to law enforcement. You can disable this feature in settings, and I strongly suggest that you do so. Bios Update For Acer Aspire One D255e Driver on this page. Like Ax. Crypt Premium, Folder Lock relies on a master password. Once youve logged in with the master password, youre free to lock and unlock files, folders, and drives without having to enter it again. Of course this should be a strong, memorable password, something that you can remember but that nobody else would guess. There is an Auto Protection option, disabled by default. If you turn this feature on, it shuts down the program after 1. You can set the timeout from one to 1. Windows, or shut down Windows, rather than just shut down the program. If youre concerned someone might try to break into your Folder Lock installation, you can enable Hack Security. At its default settings, this feature shuts down Folder Lock after three incorrect login attempts. If you frequently fumble finger your password, you may want to set a higher number. You can also configure it to log out of your Windows account or even shut down Windows altogether after a number of failed attempts. Locking and Unlocking. So, what does it mean to lock a file or folder A locked file is not encrypted. Instead, Folder Lock uses a technique called kernel level filtering to hide the locked file from Windows, and from all programs running under Windows. If that sounds a bit like the way a rootkit hides its components from Windows, well, it is quite similar, but working for good, not evil. Locked files are protected from casual snooping, which may be all you need. To lock a file or folder, you just drop it on Folder Lock. It appears inside Folder Lock and vanishes from Windows Explorer. The locking process happens in a flash, faster than encryption. You can also use a menu within the program to lock files, folders, and drives. Of course, you cant lock the Windows drive. The Lock Folders page in the programs main window lists all of your locked items, with a green padlock next to each. If youre done locking one or more items, you select them and click the button Unlock Items, or right click and choose Remove. When you do so, the item vanishes from Folder Lock and reappears in Windows Explorer. Its more likely that youll simply want to access a locked item while keeping it secure. Clicking Protection Off leaves the item inside Folder Lock, with a red open padlock icon replacing the green locked padlock. How To Remove Drawer From Hon Lateral File Cabinet. The item reappears in Windows Explorer so you can access it. You can configure Folder Lock so that when it shuts down, it turns protection back on automatically. In use, it feels somewhat similar to Ax. Crypts Secured Folders feature. Introduction To Typography Pdf there. Folder Lock doesnt just hide files and folders. It can actually hide itself as well. Just engage Stealth Mode and anybody snooping around your computer wont see a trace of it. To bring it out of hiding, you press the hotkey combination that you selected when invoking Stealth Mode. Security experts turn up their noses at security through obscurity, but this feature really can help fend off casual snoops. Encrypted Lockers. Locking items makes them invisible, but a determined hacker with physical access to the computer could conceivably still get at the data, perhaps by booting to a non Windows environment. For serious file protection, you need to create one or more encrypted lockers. These correspond to vaults in Inter. Crypto Crypto. Expert 8 and to encrypted volumes in Cypherix PE. You start by naming your locker and accepting or changing the location for the file that holds the lockers data. Next you set a password to protect the lockers contents. Like Inter. Crypto Advanced Encryption Package 2. Folder Lock includes a virtual keyboard to eliminate any possibility of password capture by a keylogger. It rates password strength as you type, but unlike Ax. Crypt its pretty forgiving. It accepted Password. Next you must choose whether to create a backup able FAT3. GB can be stored, or go for the no limits NTFS format. You also set a maximum size. The initial size on disk is much smaller, growing as needed up to that maximum. Folder Lock takes care of formatting the drive, whichever file system you use. Cypherix PE, by contrast, relies on Windows to format NTFS virtual drives.
However, not only did the Allied forces crack the code, they managed to keep that fact from the enemy, so the Nazi generals kept sharing their strategies using the faulty encryption system. The resulting intelligence served the Allied forces well. Cryptographic algorithms used today have a certain connection to the old Enigma Machine, but of course theyre totally code based, with no steampunk buttons or wheels. Unless you have the password, theres no way to decrypt an encrypted document. No, you cant just try every possible password, not unless youre willing to wait for the heat death of the universe. In 2. 00. 1, the US government settled on Advanced Encryption Standard AES. Data Encryption Standard. With even more bits in its main security key, Bruce Schneiers Blowfish algorithm should be still more secure. Youre probably familiar with symmetric encryption algorithms, where the same key encrypts and decrypts a file. AES, Blowfish, and many other common algorithms are symmetric. With this kind of algorithm, you must keep the password a deep, dark secret, and only share it via secure channels. But theres another way. In a Public Key Infrastructure system, you get two keys, one public and one private. Bit Digital Signal Controller with Flash. Recommended alternative parts. TMS320F28377S The device has SIMILAR FUNCTIONALITY but is not functionally equivalent. If I want to send you a file, I look up your public key and use it for encryption you decrypt it with your private key. Public key cryptography is less common in small scale encryption utilities. Getting Started With Folder Lock. Installation of the product is quick and simple When you do pay up, youll receive a serial number and a registration key. Keep that serial number stored in a safe place. If you forget your master password, you can unlock the program by entering that serial number. If that last statement worries you, congratulationsyouve caught on to something. All of the encryption products Ive reviewed recently have no backdoor, no way for the company to decrypt your files. But since the company clearly has your Folder Lock serial number, it could conceivably be ordered to supply it to law enforcement. You can disable this feature in settings, and I strongly suggest that you do so. Bios Update For Acer Aspire One D255e Driver on this page. Like Ax. Crypt Premium, Folder Lock relies on a master password. Once youve logged in with the master password, youre free to lock and unlock files, folders, and drives without having to enter it again. Of course this should be a strong, memorable password, something that you can remember but that nobody else would guess. There is an Auto Protection option, disabled by default. If you turn this feature on, it shuts down the program after 1. You can set the timeout from one to 1. Windows, or shut down Windows, rather than just shut down the program. If youre concerned someone might try to break into your Folder Lock installation, you can enable Hack Security. At its default settings, this feature shuts down Folder Lock after three incorrect login attempts. If you frequently fumble finger your password, you may want to set a higher number. You can also configure it to log out of your Windows account or even shut down Windows altogether after a number of failed attempts. Locking and Unlocking. So, what does it mean to lock a file or folder A locked file is not encrypted. Instead, Folder Lock uses a technique called kernel level filtering to hide the locked file from Windows, and from all programs running under Windows. If that sounds a bit like the way a rootkit hides its components from Windows, well, it is quite similar, but working for good, not evil. Locked files are protected from casual snooping, which may be all you need. To lock a file or folder, you just drop it on Folder Lock. It appears inside Folder Lock and vanishes from Windows Explorer. The locking process happens in a flash, faster than encryption. You can also use a menu within the program to lock files, folders, and drives. Of course, you cant lock the Windows drive. The Lock Folders page in the programs main window lists all of your locked items, with a green padlock next to each. If youre done locking one or more items, you select them and click the button Unlock Items, or right click and choose Remove. When you do so, the item vanishes from Folder Lock and reappears in Windows Explorer. Its more likely that youll simply want to access a locked item while keeping it secure. Clicking Protection Off leaves the item inside Folder Lock, with a red open padlock icon replacing the green locked padlock. How To Remove Drawer From Hon Lateral File Cabinet. The item reappears in Windows Explorer so you can access it. You can configure Folder Lock so that when it shuts down, it turns protection back on automatically. In use, it feels somewhat similar to Ax. Crypts Secured Folders feature. Introduction To Typography Pdf there. Folder Lock doesnt just hide files and folders. It can actually hide itself as well. Just engage Stealth Mode and anybody snooping around your computer wont see a trace of it. To bring it out of hiding, you press the hotkey combination that you selected when invoking Stealth Mode. Security experts turn up their noses at security through obscurity, but this feature really can help fend off casual snoops. Encrypted Lockers. Locking items makes them invisible, but a determined hacker with physical access to the computer could conceivably still get at the data, perhaps by booting to a non Windows environment. For serious file protection, you need to create one or more encrypted lockers. These correspond to vaults in Inter. Crypto Crypto. Expert 8 and to encrypted volumes in Cypherix PE. You start by naming your locker and accepting or changing the location for the file that holds the lockers data. Next you set a password to protect the lockers contents. Like Inter. Crypto Advanced Encryption Package 2. Folder Lock includes a virtual keyboard to eliminate any possibility of password capture by a keylogger. It rates password strength as you type, but unlike Ax. Crypt its pretty forgiving. It accepted Password. Next you must choose whether to create a backup able FAT3. GB can be stored, or go for the no limits NTFS format. You also set a maximum size. The initial size on disk is much smaller, growing as needed up to that maximum. Folder Lock takes care of formatting the drive, whichever file system you use. Cypherix PE, by contrast, relies on Windows to format NTFS virtual drives.